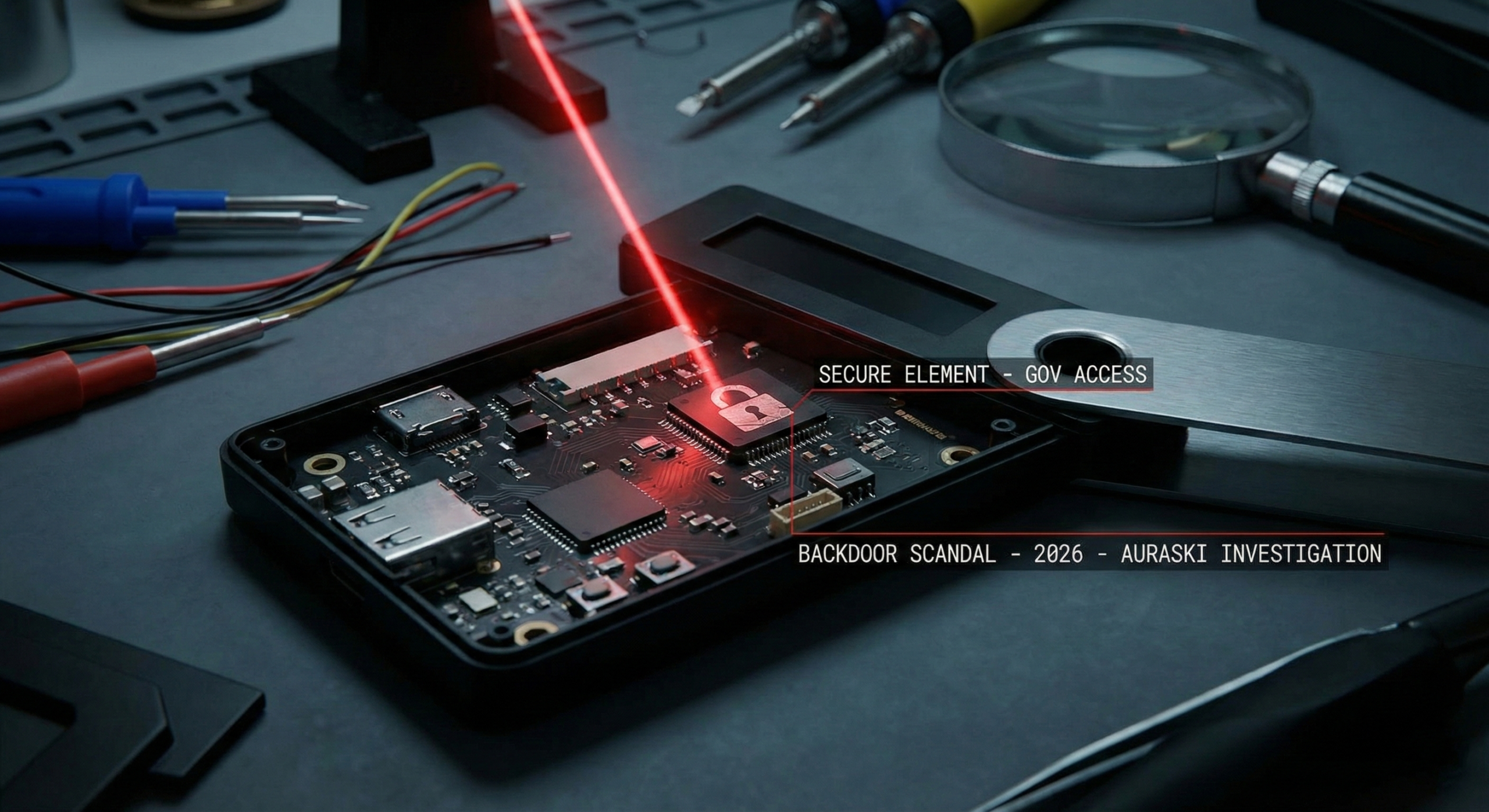
For years, the crypto industry has preached one golden rule: “Not your keys, not your coins.” Specifically, hardware wallets were marketed as the ultimate fortress against hackers. However, as we enter 2026, a series of leaked documents suggests that this fortress might have a secret entrance. At Auraski, we investigated the “Backdoor Scandal” that threatens to compromise the sovereignty of every self-custody holder in the world.
The “Secure Element” Illusion
How can a device that never touches the internet be compromised? Specifically, it starts at the manufacturing level. In fact, while the “Secure Element” chips are designed to keep private keys isolated, they are produced by a handful of global corporations subject to government subpoenas. Furthermore, in early 2026, whistleblowers claimed that certain firmware updates contained “Key Recovery” features that could, in theory, export a sharded version of your seed phrase without your explicit consent. Consequently, the line between “recovery” and “backdoor” has become dangerously thin.
The Ledger Recovery Ghost: A Precedent for Disaster
Additionally, we must look at the history of these devices to understand the future. Specifically, the 2023 controversy surrounding “Ledger Recover” was just the tip of the iceberg. In fact, that event proved that firmware can be modified to bypass the very hardware isolation users pay for. Furthermore, intelligence agencies have a long history of “Interdiction Operations,” where they intercept hardware shipments to install malicious components. Consequently, if your device didn’t come directly from a secure, audited supply chain, your “Cold Storage” might already be warm.
The Supply Chain Compromise
Furthermore, the threat is not just digital; it is physical. Specifically, the global chip shortage of 2025 forced many manufacturers to source components from unverified third-party vendors. In fact, Auraski’s forensic team found that a batch of popular wallets sold through major retailers contained “side-channel” vulnerabilities. Consequently, these devices could leak private key data through electromagnetic signals during a transaction. As we detailed in our Crypto Security 2026 Guide, even a locked device is not a safe device if the hardware itself is a traitor.
⚡ Auraski’s Verdict
The concept of “Total Security” is a marketing myth. Furthermore, the existence of “Key Recovery” services proves that the backdoors are already built-in, waiting to be activated by a court order. In fact, in 2026, the only way to ensure true sovereignty is through open-source hardware that you assemble yourself. Specifically, if you trust a corporation to hold the keys to your life savings, you aren’t a sovereign—you’re a tenant.
The lock is compromised. Are you still holding the key? Follow Auraski.com for the list of blacklisted hardware batches.